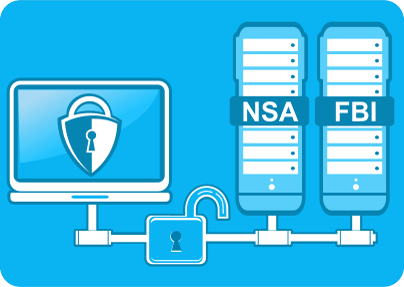
The recent document leak by former National Security Agency (NSA) contractor Edward Snowden did not only shed a different light on our favorite and trusted Internet giants, but also made us realize how fragile and illusory our concept of freedom is. The leak alleges nothing less than frontrunner Internet firms, like Google, Yahoo, Facebook, Skype, were allowing the NSA and the FBI to access their servers, that is, to check the personal files of a vast number of users around the globe. This Washington Post article gives you further details on the subject.
Even though we have always suspected and feared that the Big Brother has been watching us, to be confronted with this fact so harshly feels more than alarming. Do the recent news mean that we no longer have the basic Internet privacy protection rights?
Even though the above mentioned companies have denied allegations and to prove their transparency, published reports on how many law enforcement requests they had received, if only a fragment of the news is true, we do have a lot to worry about.
We use Skype, Google, Yahoo, Dropbox etc on a daily basis and the bulk part of our online life is based on the services they provide. They own the lion-share of the world wide web. So we (naively?) entrust our personal information, often even sensitive data to them and we do that assuming that they guarantee terms and conditions stated in their privacy policy. And unfortunately, even if you decided to stop trusting them from now on, it would be just too hard to find alternatives for all the services they offer.
So is it a hope against hope situation? Well, while there is not much to be optimistic about regarding the yet unsettled issue, you can still be proactive and safeguard your data. If you keep your information encrypted, there is not much the system can do with it.
East-Tec offers you 2 software products to fight for your Internet privacy rights in the brewing battle. east-tec SafeBit lets you create virtual disk drives for secure data storage and it also features options for secure data transfer. The virtual disk drive contains all your data encrypted but the data is displayed as if it were plain text. This means, working with the encrypted data is just like working with plain text data. This is how to create a virtual disk drive, to keep your files protected and the drive (safe) can also be emailed securely.
east-tec InvisibleSecrets is a steganography tool to hide your files, emails and sensitive information into innocent looking carriers, for instance photos, mp3 files, or websites. Those files can be securely transferred over the Internet, so this is another way to get around the threatening situation.
We hope this information proves useful in safeguarding your Internet privacy rights.