Welcome to the second installment of our Encryption series. In this post I'm going to show you how to encode your confidential data with an encryption software to protect your sensitive business, financial, or medical data, passwords, private photos, videos and so forth.
If kept on your PC in plain text format, sensitive files and folders may become easily accessible to hackers, laptop thieves, and other unwanted third parties. But properly implemented encryption guarantees that your private data remains protected even if unauthorized parties manage to have access to your PC. It is because it's practically impossible to crack a password protected advanced cipher that was used to encode your original message.
east-tec SafeBit employs the most advanced algorithm, AES Rijndael, that has been approved by the US government for sensitive data encryption and never been cracked. The software creates Safes (virtual drives) that automatically encrypt any file/folder you place into them. This is a much handier way to encrypt multiple files and folders than encoding them one by one. For extra security and easy access, the Safes can be uploaded to your cloud storage.
And now let me walk you through the few easy steps required to encrypt your confidential files and folders in a Safe created by the software.
To get started, open east-tec SafeBit and select New Safe.

Then click Create New Safe.

In the resulting window name your Safe for easy identification and provide a password for security protection.
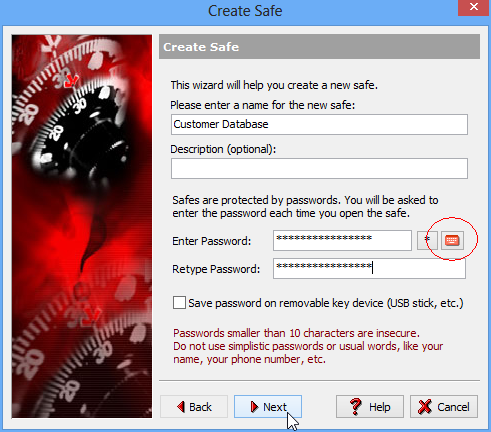
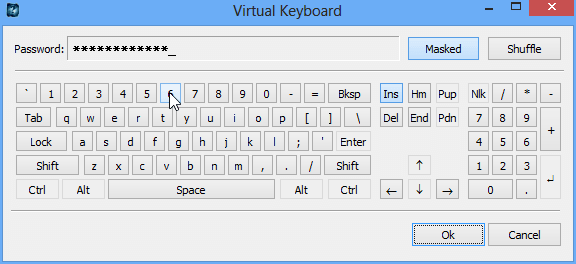
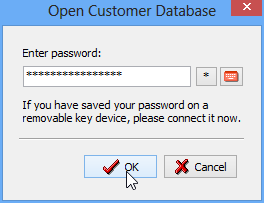
For extra security (keylogger protection) you can use the built-in Virtual Keyboard and enter your password by clicking the characters of it using your mouse. The Virtual Keyboard is available by clicking the small red keyboard icon next to the Enter Password field. (circled on the screenshot above). Click OK when your are done entering your password.
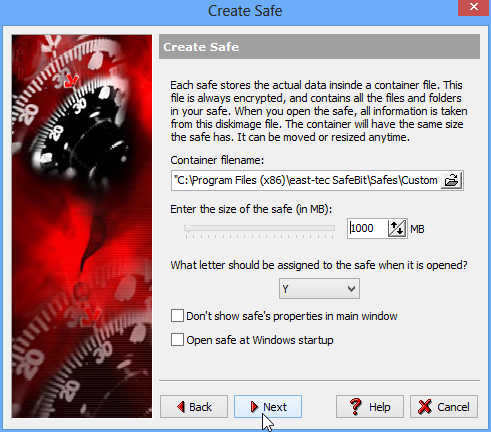
You will be then asked to confirm your password. When done, click Next. In the resulting window you can set the location, size and assigned letter of your Safe (for easy setup you can use the default settings). When done click Next.
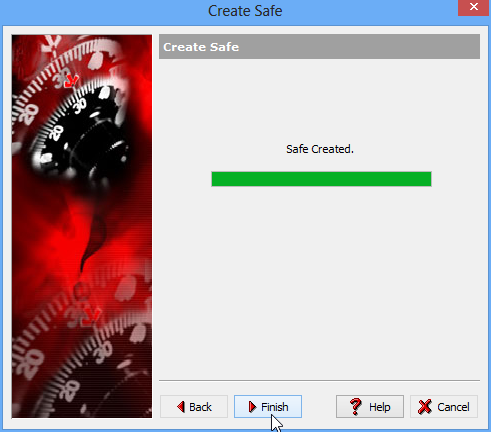
The resulting window confirms that the Safe has been created. Click Finish to exit.
Now your Safe is ready to be used and you can start moving your sensitive files/folders into it for encryption and password protection. Let me show you how to do it.
Open your newly created Safe.

Enter the Safe's password
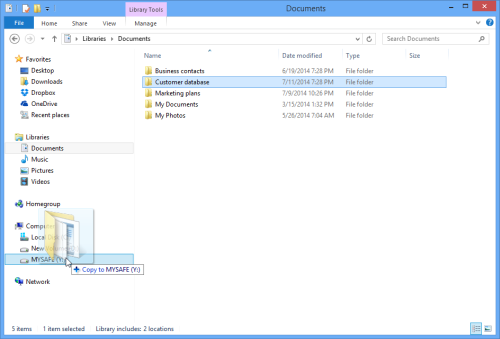
Now your Safe is open. Open Windows Explorer and locate the files/folders you want to securely store in the encryption Safe...
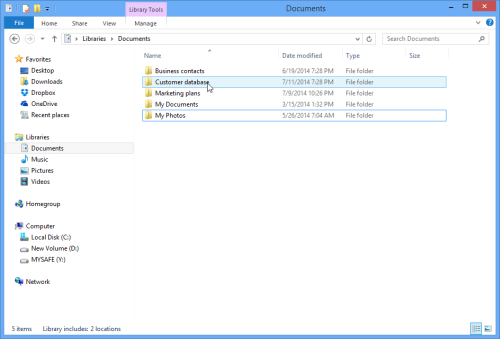
...and use the usual drag and drop to move them to the Safe.
If you double click your Safe in Windows Explorer MYSAFE(Y) you can see that the file (Customer Database) has been moved to it.
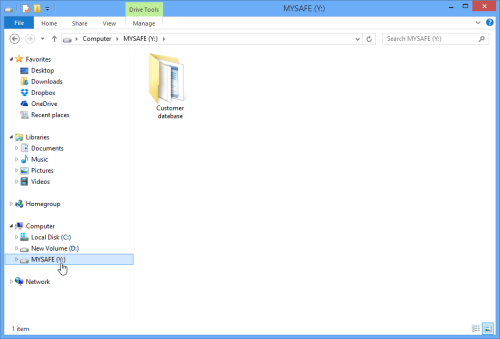
The folder appears like normal data to you, but actually it is encrypted with the secure AES Rijndael algorithm. This feature is called on-the-fly encryption and it is meant to help you work with encrypted data as if they were usual files/folders, but with the added protection of encryption. As soon as you finished working with the files/folders in the Safe and you close it, the Safe disappears from Windows Explorer's drive list for extra security. You can be rest assured that the Safe stores your confidential data encrypted and password protected against third party access. When you need to work with the data again, you just need to run the software and you can open the Safe from its interface.
Now there is only one important step left: the shredding of the original files/folders that are still on your hard drive in unencrypted format. That can easily be managed with east-tec Eraser.
This way your sensitive files can be encrypted, password protected and the original data destructed beyond recovery. Now your sensitive files and folders are securely protected against any third party intrusion, or in case of laptop theft, or loss.

